In the ever-evolving landscape of breaches and cybersecurity, we have again to come to terms with more bad news for those still believing in the mantra of 2018, “We value your privacy.” It seems impossible to avoid the news of some sort of breach or hack, but they’re coming particularly hard and fast in the last month. Some of the more recent breaches and hacks involve some of the biggest and best companies in the world so let’s see what is happening with the latest developments in cybersecurity and how it will affect the companies and the customers involved.
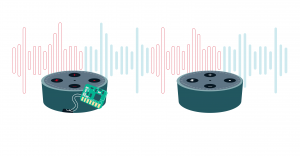
Amazons flagship piece of technology, Alexa, is one of Amazon’s most important products. Despite Alexas popularity, the smart assistant has carried some privacy concerns for quite some time. Earlier this year Alexa sent a private user conversation to contact randomly and without any consent. This was the first in a series of worrying signs that Alexa could essentially be used as a glorified piece of spyware. This was initially dismissed by most as conspiratorial.
Now we see that not only is it possible, but it already exists. Hackers at DefCon managed to turn an Alexa into a hacked listening device it has been reported, “The hack involved a modified Amazon Echo, which had parts swapped out, including some that had been soldered on. The modified Echo was then used to hack into other, non-modified Echos by connecting both the hackers’ Echo and a regular Echo to the same LAN.”
This allowed the hackers to turn their own, modified Echo into a listening bug, relaying audio from the other Echo speakers without those speakers indicating that they were transmitting. An Amazon spokesperson told Wired that “customers do not need to take any action as their devices have been automatically updated with security fixes,” and that “this issue would have required a malicious actor to have physical access to a device and the ability to modify the device hardware.”
Social media has a stronger need for cybersecurity to protect democracy.
Facebook is intending on doing some of the most proactive work for the safety and cybersecurity of their users in the company’s history. With all of the headlines and bad press dedicated to bashing the service into action, it seems that the company is keen to avoid another political mudslinging contest like the 2016 US Elections. To prevent disinformation attempts before the midterm elections this year, Facebook has set up a “war room” to conduct real-time analysis of the types of content being posted in the coming months looking for any bot-like behavior or anything unusual relating to spreading fake news and political disinformation. A dedicated team of cybersecurity experts will be on hand to monitor the war room until the election cycle is finished.
It’s not just these efforts that show a commitment to turning the tide against disinformation, but how Facebook has conducted themselves since the 2016 election cycle, “Facebook took down almost 1.3 billion fake accounts in the last six months alone, and has routinely highlighted the number of fake accounts it takes down ahead of foreign elections. (For context, Facebook has about 2.2 billion monthly active users, and the company has estimated in the past that 3-4 percent of those are “false accounts.”) Before France’s presidential election in early 2017, Facebook deleted 30,000 fake accounts.”
Twitter has also made a landmark decision to remove a lot of the original APIs that existed on the platform for third-party integrations to be removed, thus eliminating a huge source of bot behavior on the platform. Essentially, what it means for the 6 million users who used third-party APIs, like Tweetbot, is that “The changes mean that Tweetbot’s timeline streaming is now disabled, so timelines will refresh every one to two minutes instead–a loss for people who want to see new tweets in real-time. Push notifications for Mentions and Direct Messages will also be delayed by a few minutes, while push notifications for Likes, Retweets, Follows and Quotes have been disabled altogether.”

Real world consequences of bot based attacks.
The healthcare sector is in a unique situation that necessitates an idea of just how frequent and severe and challenging hacks are as TechCrunch reports “FortiGuard Labs, a major security protection firm, reports that in 2017, healthcare saw an average of almost 32,000 intrusion attacks per day per organization as compared to more than 14,300 per organization in other industries.” On top of the frequency of the attacks, there is a unique problem that attacks on the healthcare sector that makes it uniquely vulnerable to phishing attacks, the risk of killing patients. The average healthcare facility has a network for the infection to spread into as healthcare facilities have multiple connected medical devices and equipment, from ventilators, X-ray and MRI machines, medical lasers and of course radiation treatment.
Now with IOT technology so prevalent in so many sectors are improving efficiency and productivity but simultaneously the companies have opened themselves to a new type of attack in their infrastructure. MaDioT attacks involve remotely hacking smart devices such as a thermostat or air conditioner and using the increase in power to shut down electrical grids by causing line failures, triggering a blackout. The amount of effort it takes to construct this type of attack? 200 bots. This number is maddeningly low and as of right now this is exploitation is currently without a fix as Ars Technica reported “Using a simulation of the power grid of the Western System Coordinating Council—the grid that serves most of the western United States—a 30-percent increase in demand across the grid could cause all of the generators in the grid to trip and go offline. “For such an attack, an adversary requires access to about 90,000 air conditioners or 18,000 electric water heaters within the targeted geographical area.”
Cybersecurity is essential for us to protect our growing vulnerabilities as we increasingly integrate technology into every part of our lives. Frauds, fake news pedlars and bad actors content to interfere with the democratic process are a presence that will be haunting the internet for quite some time, and the story that seems to be emerging is that there will always be new ways to exploit new technology.